PRIMARY CATEGORY → WEB TECHNOLOGIES
Discovery | Footprinting | Enumeration
Agent Login Panel
<URL>/scp/login.phpDetecting an OSTicket Site
Websiteiiiiiiii Footer
Almost, most of the OSTicket installations will showcase the OSTicket logo followed by the phrase Powered by in the page’s footer
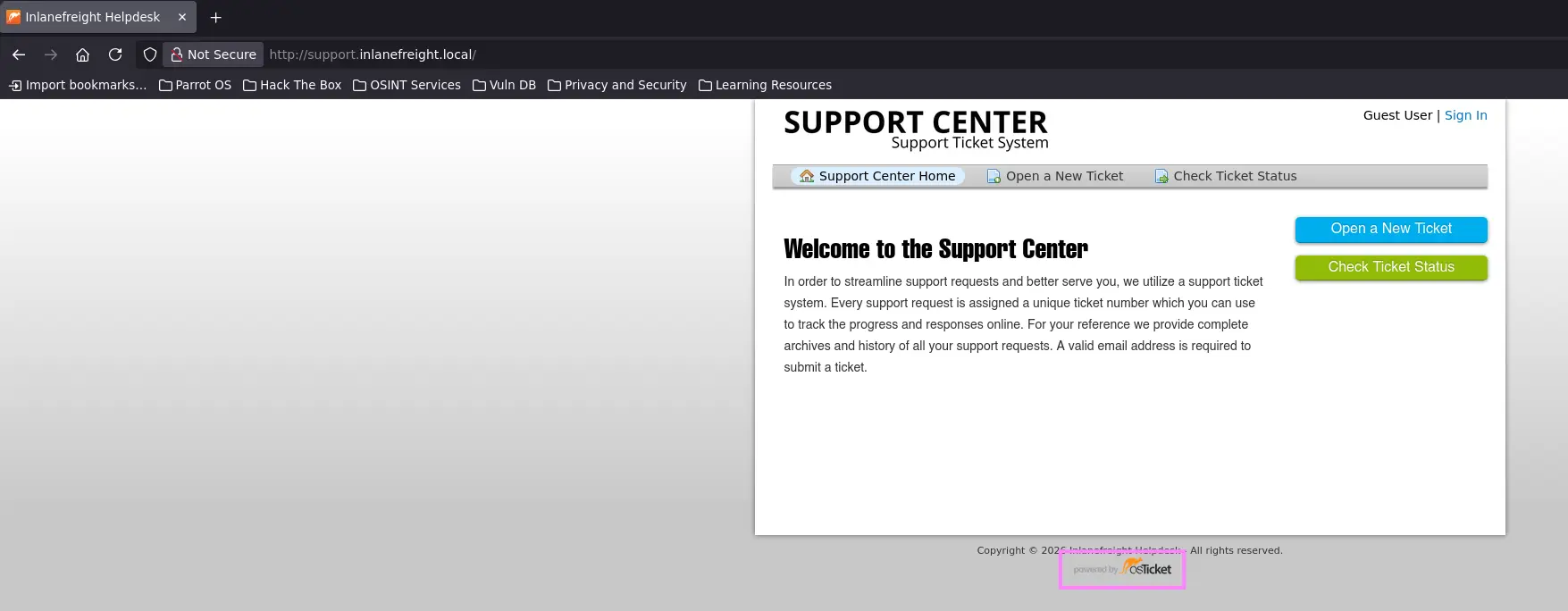
Zoom in
We can send an HTTP request as well and filter the response as follows
curl --silent --location --request GET '<URL>' | grep -i --color -- 'osticket'Attacking OSTicket
Abusing Temporary Email Accounts assigned to Tickets
Let’s suppose we find an exposed service such as a company’s Slack or Gitlab, which requires a valid company email in order to register a new account and join the organization
On the other hand, we discover another target that is running an OSTicket web application where users can sign up and log in to create any type of ticket related to an inquiry
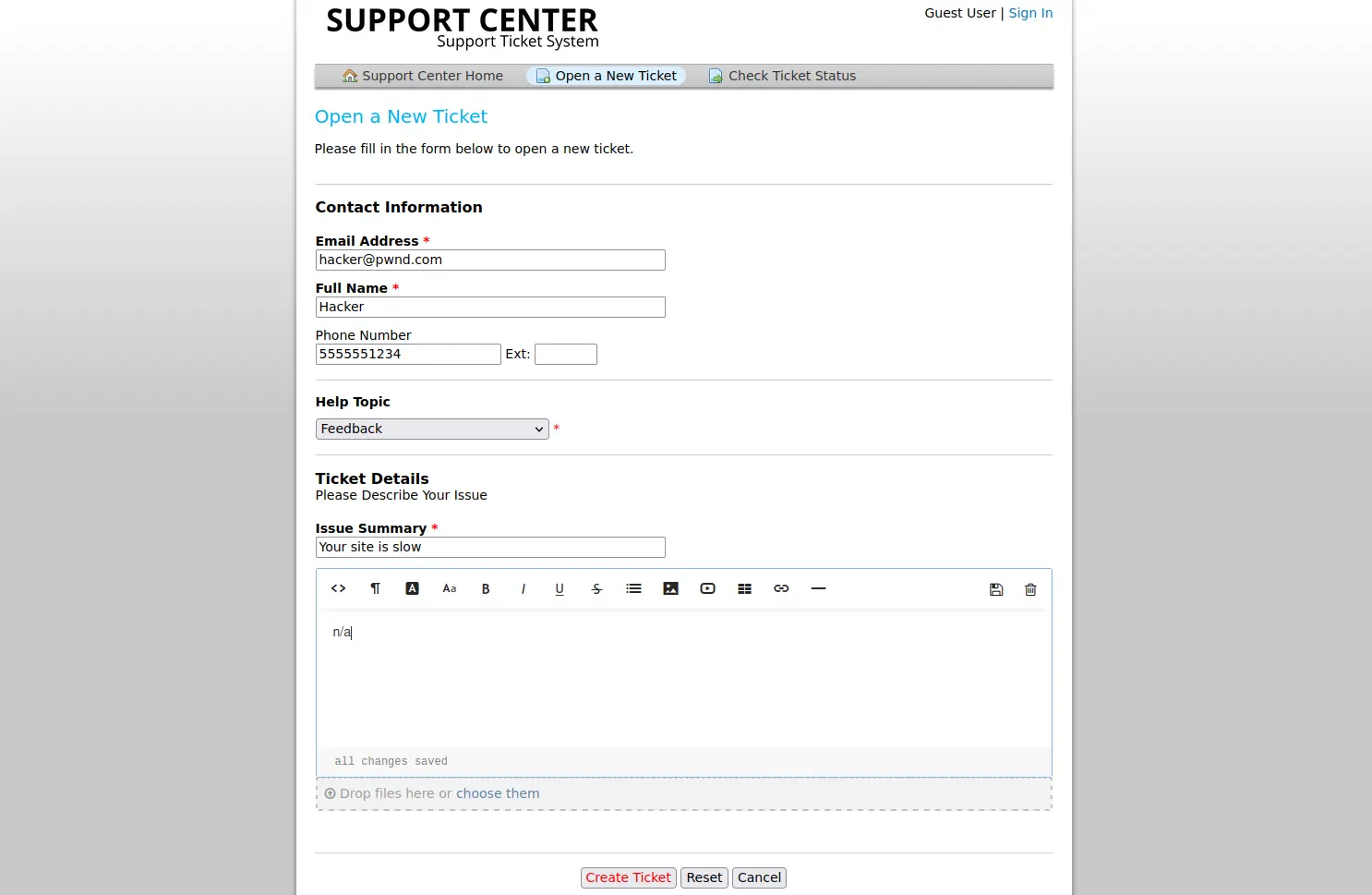
Zoom in
After creating an account on the support platform and log in, we realize that a temporary email account is assigned to the new ticket
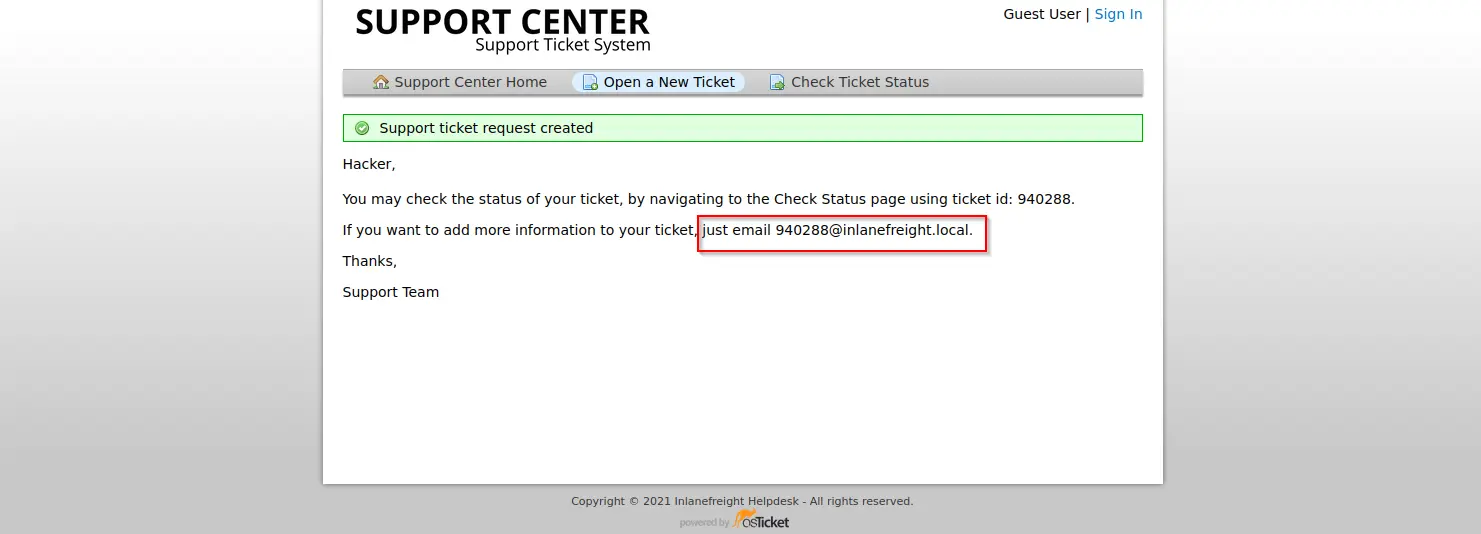
Zoom in
We can enter the Ticket ID to check its status and all the information related to it. This time the company set up their helpdesk system ( OSTicket ) to correlate ticket numbers with emails, so any email sent to this account will appear in the menu below
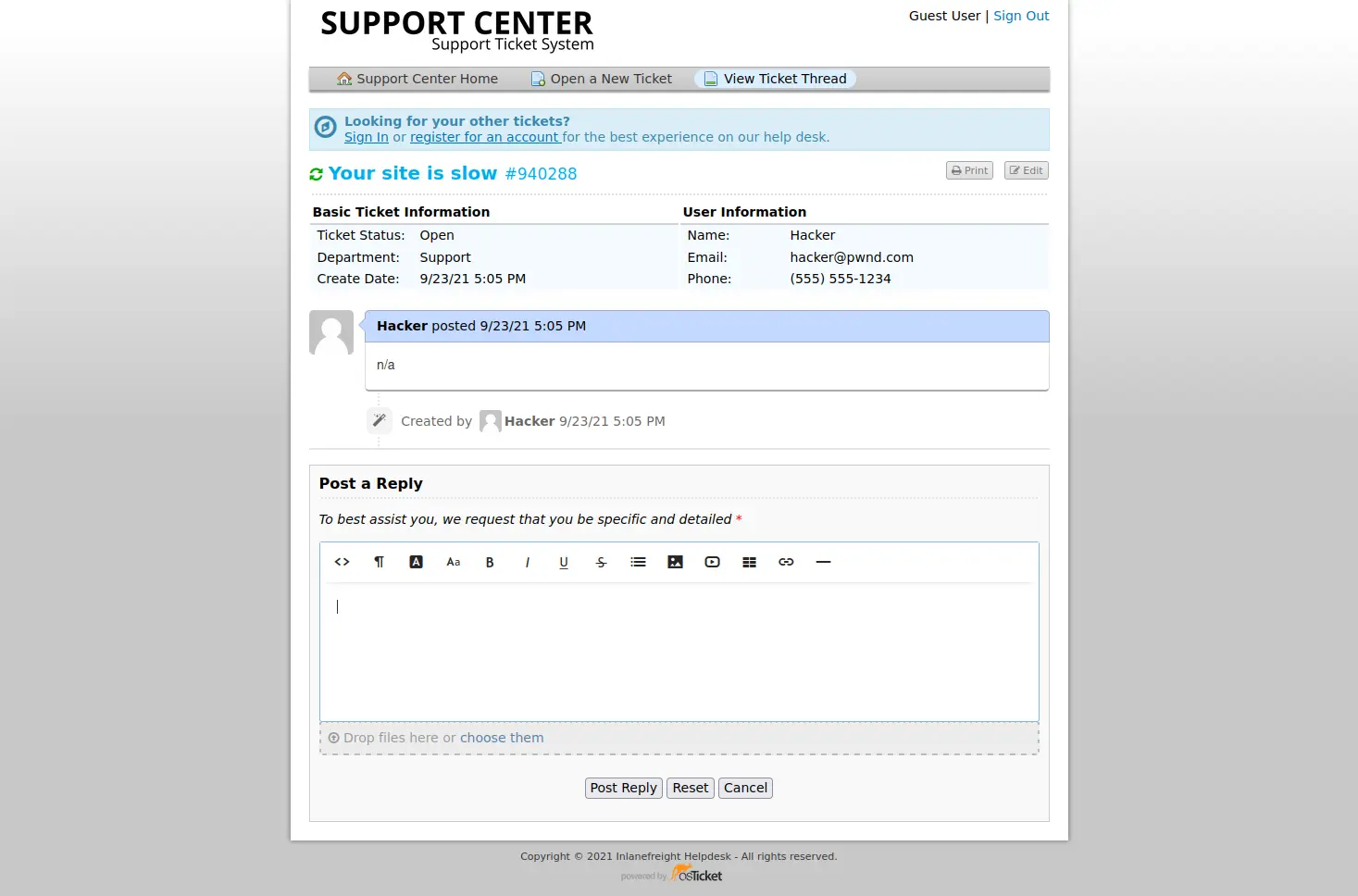
Zoom in
Therefore, we could access to the Gitlab instance’s login page and select the Register now option as we do not have valid credentials for an existing account
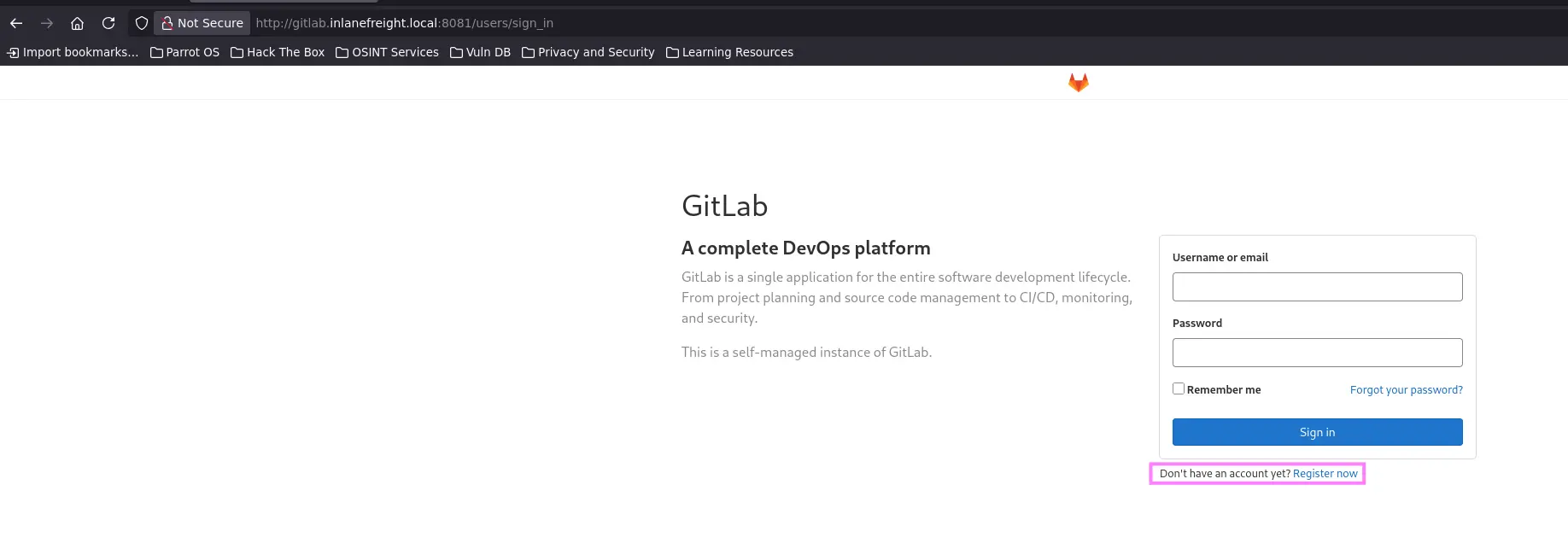
Zoom in
However, we can sign up using the email account associated with the ticket
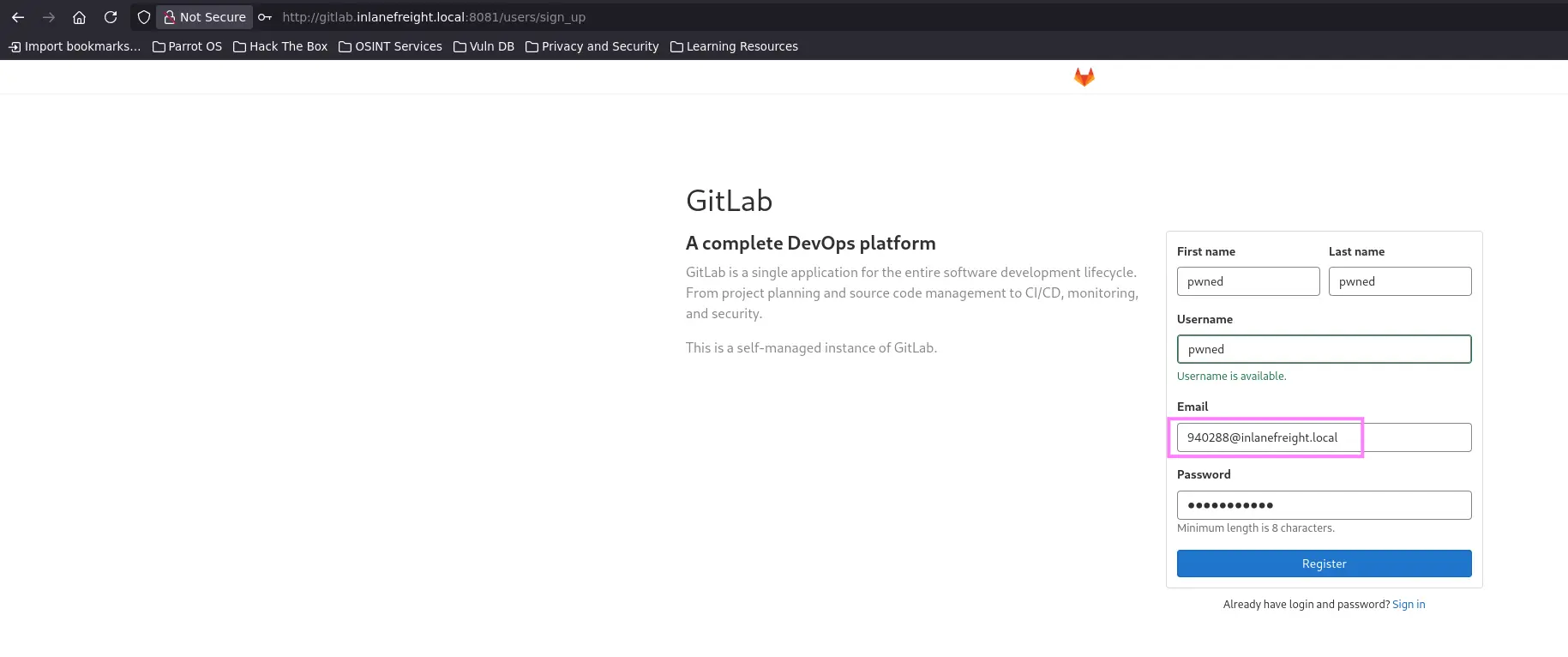
Zoom in
Once we are logged in, we may uncover certain repositories which only accounts of the given company have access to