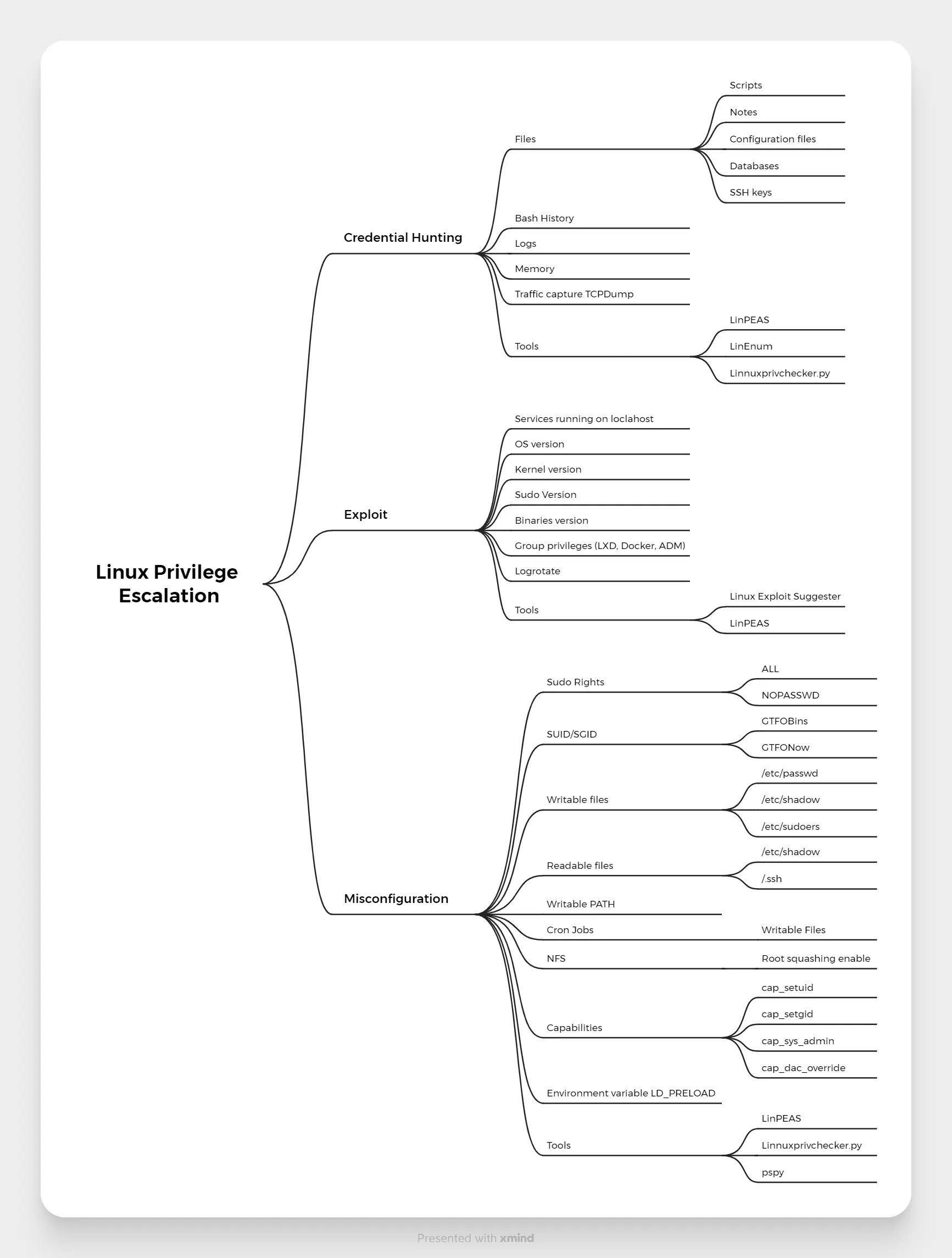
PRIMARY CATEGORY → CHECKLISTS • LINUX PRIVESC
Mindmap
Zoom in
Global
- Additional NICs pointing to other subnets (
ip a s,/sys/class/net) - Interesting System Directories (
/<DIRECTORY>,/opt,/varand so on ) - Running Services that are not externally accesible (
netstatorss) and are running as a different user ( More privileged or Root ) - Credential Hunting on Configuration Files (
/etc,/etc/fstabor web directories →/var/www/worpdress/wp-config.php) - Credential Hunting in Network Traffic
- Cron Jobs: Monitor Processes with Pspy and check
/etc/cron.XXXand/var/spool/crondirectories - List current Processes
- SUID/SGID Binaries (Pwnkit as well)
- Capabilites
- Logged in Users
- Kernel Vulnerabilities ( e.g. OverlayFS, Dirty Pipe and so on )
- Sudo version vulnerability
- Installed Packages Vulnerabilities ( See Screen and Logrotate )
- Readable Shadow File (
/etc/shadow) - Password Hashes on
/etc/passwd - Unmounted FS and Additional Drives
- Writable Docker Socket Files
- TMUX or SCREEN sessions ( Write permissions on the given socket )
- NFS Shares with NO_ROOT_SQUASH enabled
- Check RUNPATH Hijacking if there is a privileged ( SUID, Sudo, Capabilities… ) custom binary ( ELF )
- Wildcards abuse if TAR is used in a privileged way ( e.g. Sudo or Cron Job )
- Trace System Calls of custom and privileged binaries
- Run Privesc Enumeration Scripts such as LINPEAS
Per User
- Sudo Privileges
- Privileged Groups to which the user belongs to ( e.g. Docker, LXD, Disk and so on)
- Look for Sensitive Files on Current User’s home directory ( e.g. Shell History Files, SSH Keys and so on )
- Current User’s Home Directory ( History Files, .SSH Directory )
- Mounted FS and Drives
- Interesting Resources ( Hidden, Writable, Owned, Temporary, Scripts… )
- Access other system user directories within
/homedirectory - Enviromental variables and parameters
- See Python Library Hijacking if the current user has sudo privileges on a Python Script or Cron Job runs it as a privileged user
- LD_PRELOAD Abuse → Sudo Privileges on an ELF Binary
- See Escaping RShells if we land on a restricted shell
- See Docker Abuse if we land on a docker container
- See K8S Abuse if we land on a K8S container
- Check Environment Enumeration