PRIMARY CATEGORY → MITM & COERCED AUTHS
Theory
WPAD
The Web Proxy Auto-Discovery Protocol ( WPAD ) allows a web client to automatically discover a proxy configuration
To do so, the client search for a WPAD.dat file in the following ways →
- DHCP ( 252 Option )
- DNS → Query name to the Primary DNS Server trying to resolve
wpadorwpad.domain.internal - ANYCAST Protocols as a fallback
By default, any Windows host has the Automatically detect Proxy settings option enabled in Internet Options
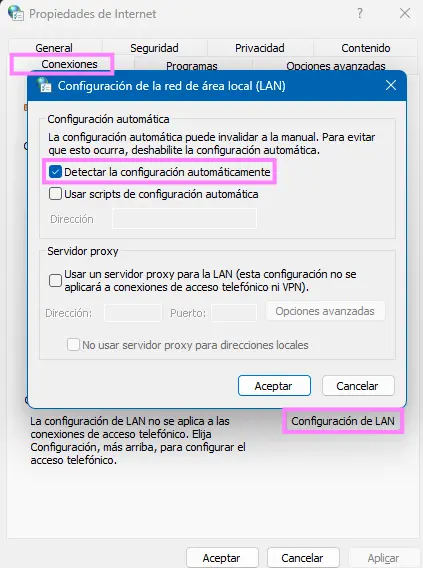
Zoom in
Therefore, a Windows client search for a proxy configuration automatically by trying to discover a PAC file
As stated, this discovery is carried out through DNS, DHCP or an ANYCAST protocol
Once the name resolution is completed and the client knows the IP Address of the given proxy server, it tries to download via HTTP a JS PAC file, which is a file containing all the configuration related to the proxy server
http://wpad.domain.local/wpad.datHowever, if an operator controls the client DNS resolution, either through DHCPv6 Spoofing or by being able to create a WPAD DNS record in the domain zone, and points the WPAD record to the IP Address of a machine under his control, the given client can be forced to establish a connection to the latter
Moreover, this connection requires a subsequent authentication, so an attacker could set up an HTTP server in order to receive the incoming authentication and capture the Net-NTLMv2 hashes or perform a NTLM Relay attack
Global Query Block List
To prevent this issue, Microsoft introduced a Global DNS Query Block list starting with Windows Server 2008. By default, this list contains two values →
- WPAD
- ISATAP ( Intra-Site Automatic Tunnel Addressing Protocol ). Also vulnerable
Therefore, any client that sends a query name containing wpad.domain.internal to the DC will receive an NXDOMAIN response indicating that the provided name does not exist, even if it really exists
This means that if an attacker manages to create a DNS record named WPAD in the domain DNS zone pointing to itself, it will not have any effect at all
