PRIMARY CATEGORY → CHECKLISTS • WINDOWS PRIVESC
Mindmap
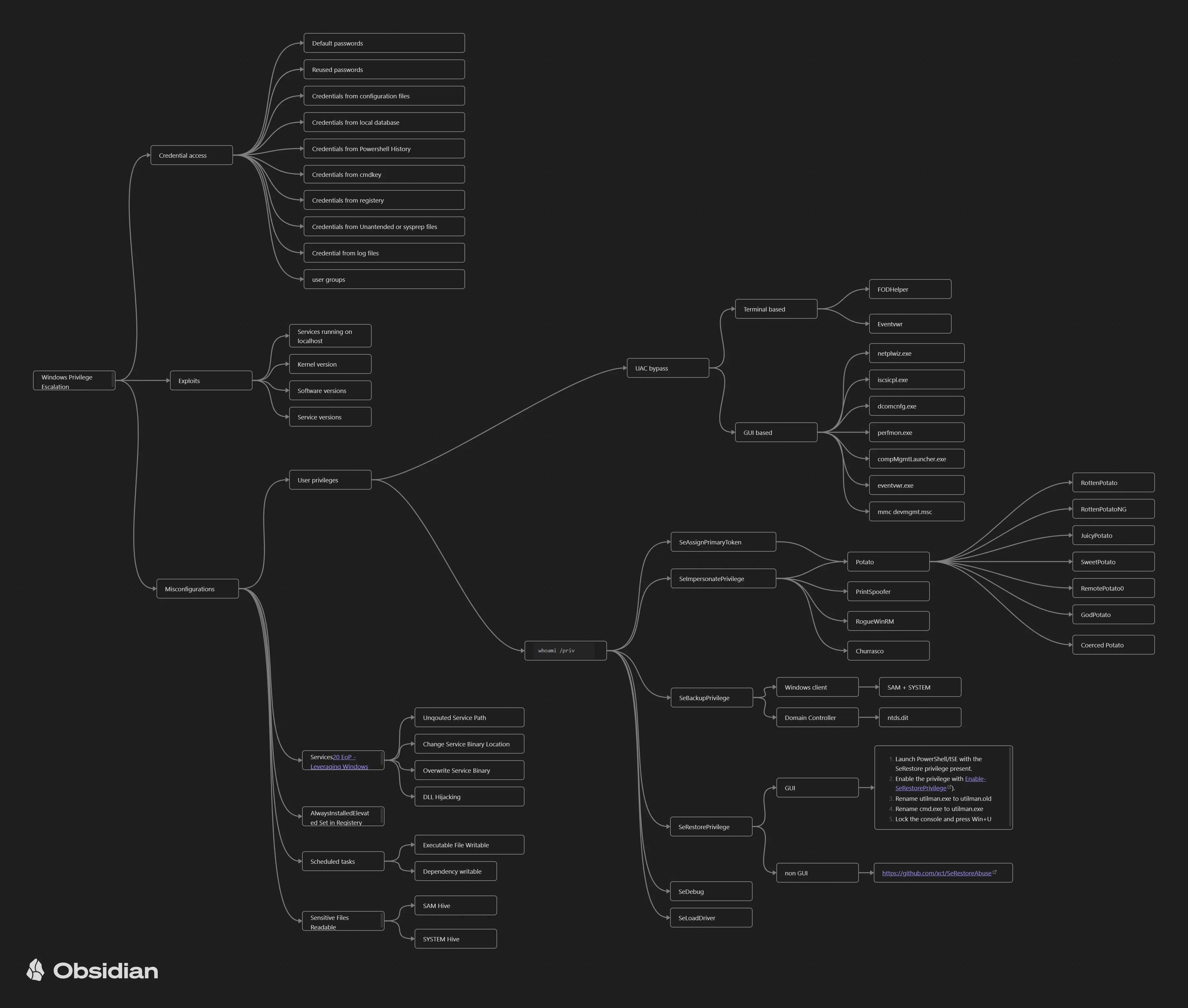
Zoom in
Non-Privileged
e.g. Network Interfaces, ARP Table, Routing Table…
-
Is the current system a domain-joined machine?
e.g. HTTP ↔ 8000 TCP Port ( 127.0.0.1:8080 )
- SeImpersonate and SeAssignPrimaryToken Privileges
From LOCAL SERVICE or NETWORK SERVICE to LOCAL SYSTEM
RoguePotato ↔ RottenPotato ↔ JuicyPotato ↔ PrintSpoofer
- Other Sensitive Windows Privileges related to the Current Access Token
e.g. seDebug, seBackup, seLoadDriver and so on
-
Local and Domain Privileged Groups to which the Current User belongs
e.g. A local user account named Alex which belongs to Backup Operators
e.g. MRemoteNG
Sherlock ↔ Windows Exploit Suggester
Netexec ↔ Impacket’s REG.py ↔ Get-GPPAutologon
-
Directory Content Checking → C: | Program Files | Program Files (x86) | Users
-
Leaked Credentials on Local Users or Computer Description
-
Look for Powershell Credential Objects
e.g. Resources containing juicy strings such as “pass|password|passwd” and so on
See also Other Interesting Files and Unattended Installation Files
-
Credential Extraction from Browsers ( Chrome, Firefox… )
e.g. Cookies, Saved Logins…
-
Credentials stored in Windows Vault and Credential Manager
See DPAPI Abuse
-
Coercion through a Shortcut File Upload if the current user has WRITE permissions over interesting and busy local folders or shares
-
UAC Bypasses if needed
-
For any Microsoft Exchange Server deployed, see Sensitive Information Extraction from Microsoft Exchange Inbox
-
Check for ADS in files
-
List existing Scheduled Tasks
-
Existing Named Pipes with wrong DACLs (e.g. Everyone → Write Permissions )
-
If we land on a CITRIX Windows Restricted Environment, see CITRIX Breakout
Privileged
- Windows Credential Dump - NTDS | SAM | SYSTEM | SECURITY | LSASS
Impacket’s Secretsdump.py ↔ Mimikatz ↔ Netexec
- Credentials for all system users stored in Windows Vault and Credential Manager
See DPAPI Abuse
Impacket’s Secretsdump.py + ( Hashcat + John )
-
If the victim has a Wireless Netword Card, see WiFi Credential Extraction
Credentials for all system users